How is cloud security defined?
Cloud computing security, commonly called cloud security, refers to a collection of practices, policies, technologies, and services that protect cloud data, applications, and infrastructure from cyber threats or reduce their impact.
Cloud security is essential for any company undergoing digital transformation and relying on managed cloud services. It provides protection against both external and internal threats.
How do cloud service providers ensure your security?
Cloud security depends on several factors: the type of cloud environment (public, private, or hybrid), software reliability, provider trustworthiness, service configuration, access control policies, and user awareness.
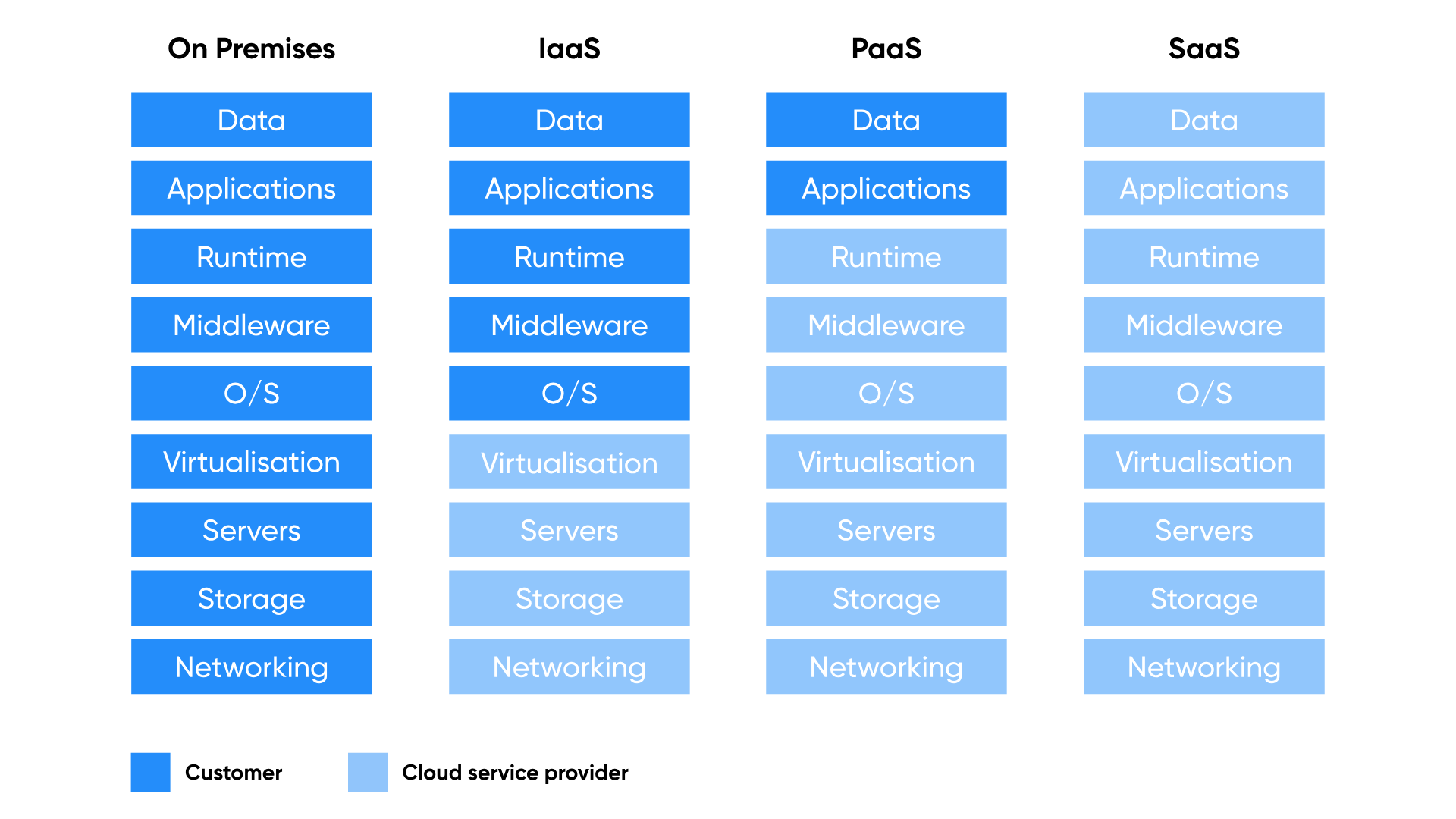
Importantly, cloud security is a shared responsibility between your organisation and your cloud provider. Providers deploy comprehensive cybersecurity tooling to protect customer data, reducing the burden on your internal team.
Here are five ways cloud security solutions reduce business risk:
- Data protection. Automated detection and encryption continuously monitor and protect data as it moves across workloads, ensuring compliance with standards without requiring deep knowledge of each regulation.
- Compliance and data privacy. Cloud environments offer a comprehensive view of your compliance posture, with automated checks and timely updates aligned to your industry's regulatory requirements.
- Continuous threat detection. Integrated threat intelligence, anomaly detection, and machine learning identify and stop malicious or unauthorised traffic before it becomes a business-impacting incident.
- User and device access management. Cloud platforms handle user authentication, authorisation, and single sign-on, scaling identity and access management capabilities as your organisation grows.
- Network and application security. Fine-grained security policies, vulnerability scanning, and continuous monitoring help detect issues early without straining limited in-house resources.
7 cloud security activities your organisation must maintain
Even with a strong cloud provider, your organisation plays a critical role in security. Here are the key activities to keep active:
- Install up-to-date antivirus software and identity management tools on all devices.
- Configure a firewall to block suspicious traffic.
- Run regular vulnerability scans on hardware and software, and apply patches promptly.
- Perform daily backups, covering files, databases, operating systems, applications, virtual machines, and cloud-hosted infrastructure.
- Comply with data privacy regulations relevant to your industry and geography.
- Enable rapid identification of security alerts and root-cause analysis.
- Maintain and regularly test a comprehensive backup and recovery plan.
If these activities are difficult to manage with your current infrastructure, moving to the public cloud, supported by a trusted partner like Baltic Amadeus, can significantly improve your organisation's security posture and resilience. Book your consultation.